At Deepwatch, " Empowering Your Digital Defense, Ensuring Your Peace of Mind"

Cryptography is a conversion of plain readable text into an unreadable form. In cryptography first, the data is converted into ciphertext (that is encryption) and then the ciphertext is converted back into readable form (that is decryption). Cryptography basically works on the concept of encryption and decryption. Encryption and decryption should not be confused with encoding and decoding, in which data is converted from one form to another but is not deliberately altered so as to conceal its content. Encryption is achieved through the algorithms. These algorithms are works with logic, mathematics calculations and its complexities.
Encryption: Encrypted data is referred to as ciphertext. Cyphertext is a conversion of readable text into an unreadable form. It is the most effective way to achieve data security. To read an encrypted file, you must have access to a secret key or password that enables you to decrypt it.
Decryption: Decryption is the process of converting encrypted data back into its original form, so it can be understood. To decrypt the data one needs a secret key or password so it can be decrypted.
Encryption can be done in three ways:
Symmetric: Symmetric encryption’s job is to take readable data, scramble it to make it unreadable, then unscramble it again when it’s needed. It’s generally fast, and there are lots of good encryption methods to choose from. The most important thing to remember about symmetric encryption is that both sides—the encrypter, and the decrypter—need access to the same key.
Asymmetric: Asymmetric encryption also takes readable data, scrambles it, and unscrambles it again at the other end, but there’s a twist: a different key is used for each end. Encrypters use a public key to scramble the data, and decrypters use the matching private (secret) key on the other end to unscramble it again.
Hash: Hashing is what is actually happening when you hear about passwords being “encrypted”. Strictly speaking, hashing is not a form of encryption, though it does use cryptography. Hashing takes data and creates a hash out of it, a string of data with three important properties : the same data will always produce the same hash, it’s impossible to reverse it back to the original data, given knowledge of only the hash, it’s infeasible to create another string of data that will create the same hash (called a “collision” in crypto parlance). hash is to authenticate otherwise clearly-transmitted data using a shared secret (effectively, a key.) The hash is generated from the data and this secret so that only the data and the hash are visible; the shared secret is not transmitted and it thus becomes infeasible to modify either the data or the hash without such modification being detected.
Now, there are very simple methods to achieve cryptography in our day to day life so that our data sharing can be done securely.
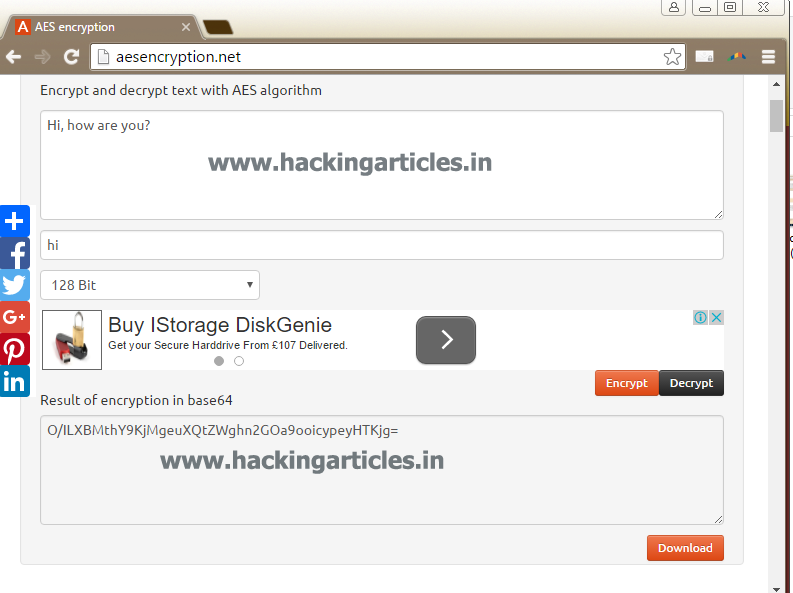
For Symmetric encryption we can simply visit the website: www.aesencryption.net, shown below :

On this website in the first box writing your message and in the second box give your password and then click on the encrypt button on the right side.

The website will now reload itself and will provide you with the encrypted text. Send this encrypted text to the desired person and tell them the key (which, in this case, is time).
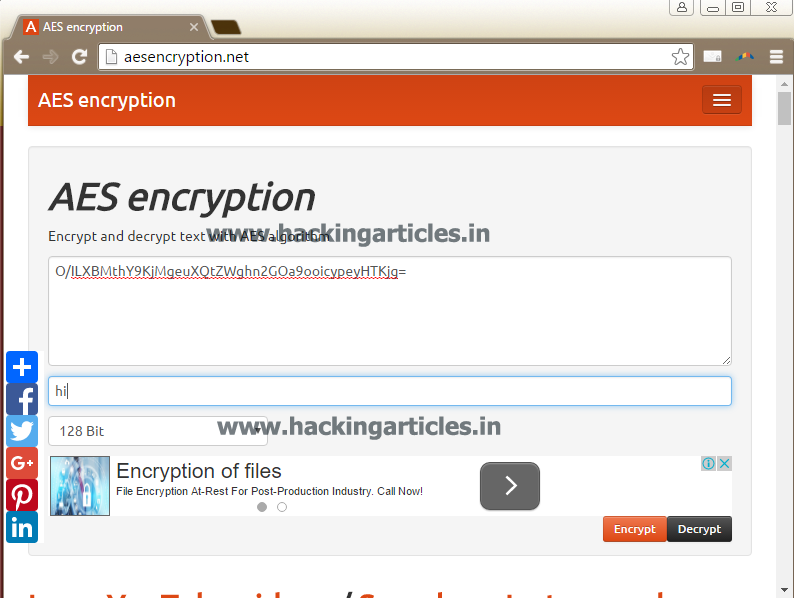
The said person, after receiving your encrypted message, can come on this website to decrypt it. He/She will simply have to copy the encrypted text and paste it on the first box and enter the key in the next box and click on the decrypt button on the right side as shown below :
After clicking on decrypt the site will reload itself and will provide you with plain text.
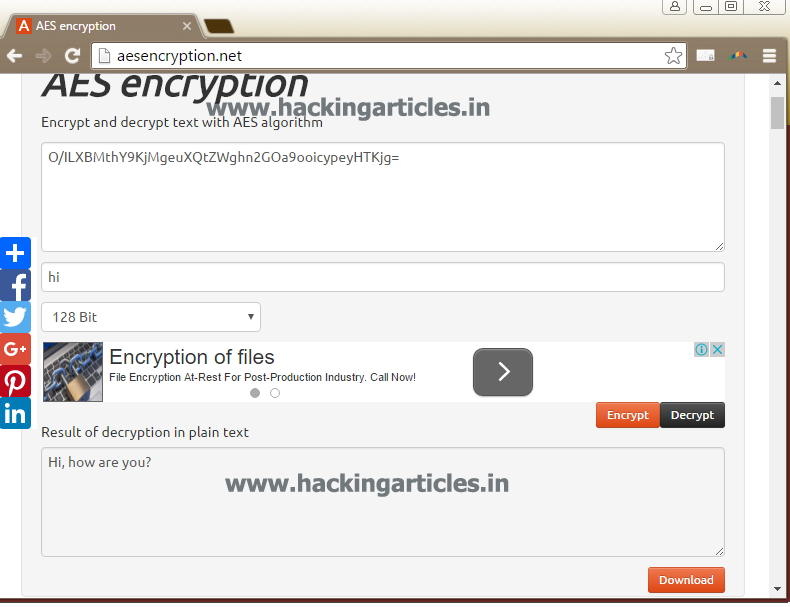
Hence, symmetric encryption.
For Asymmetric encryption, we can simply go to www.igolder.com/pgp/generate-key/, the following website will open

Click on generate PGP keys, after opening the website. A public and private key will be generated.

Now, copy the public key and click on PGP encrypt message option, it will redirect to the following page
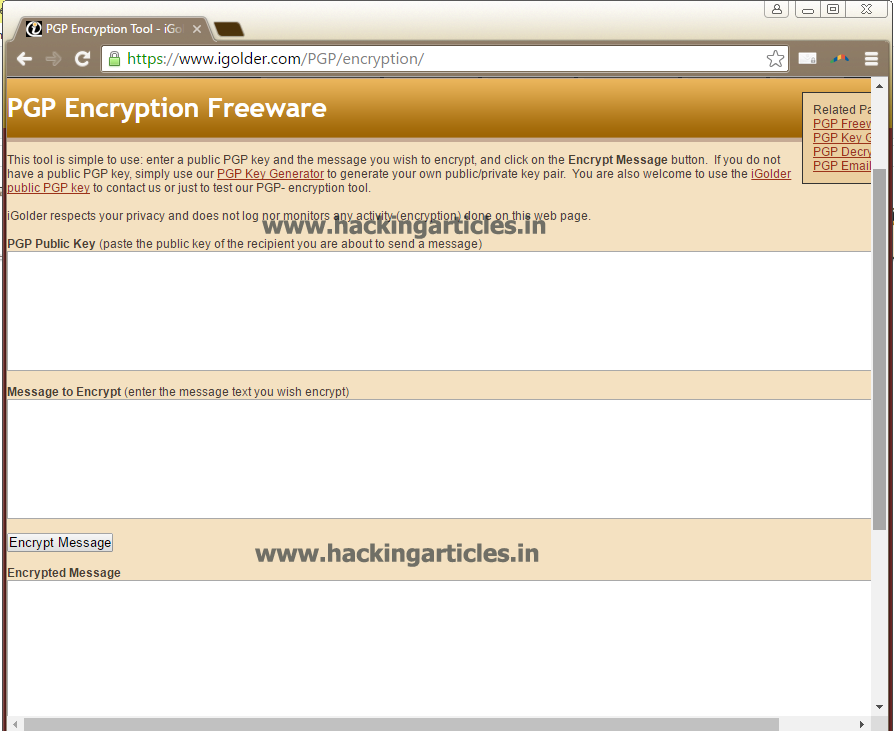
Paste the public key in the first box and write your message in the second box. By clicking on Encrypt Message, you will get your message encrypted.

Now, copy this encrypted message to the desired person along with the private key which you generated in the first step. The same person can also visit this site and click on PGP decrypt message option to decrypt the message. After clicking on the said option, the following page will open:
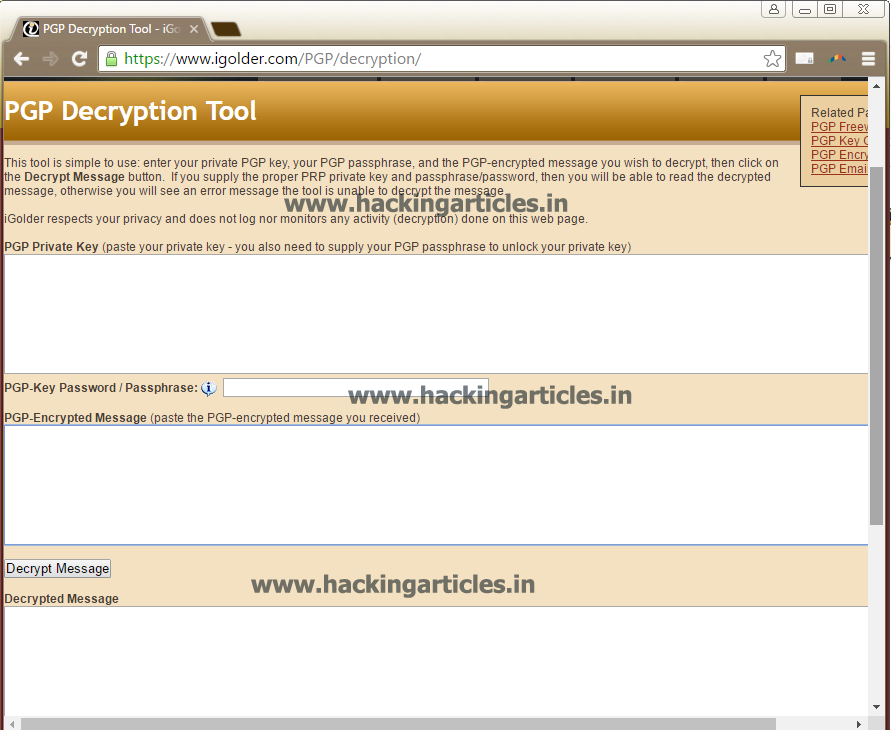
He/She can copy the private key and encrypted message and paste it on the first and second box respectively.
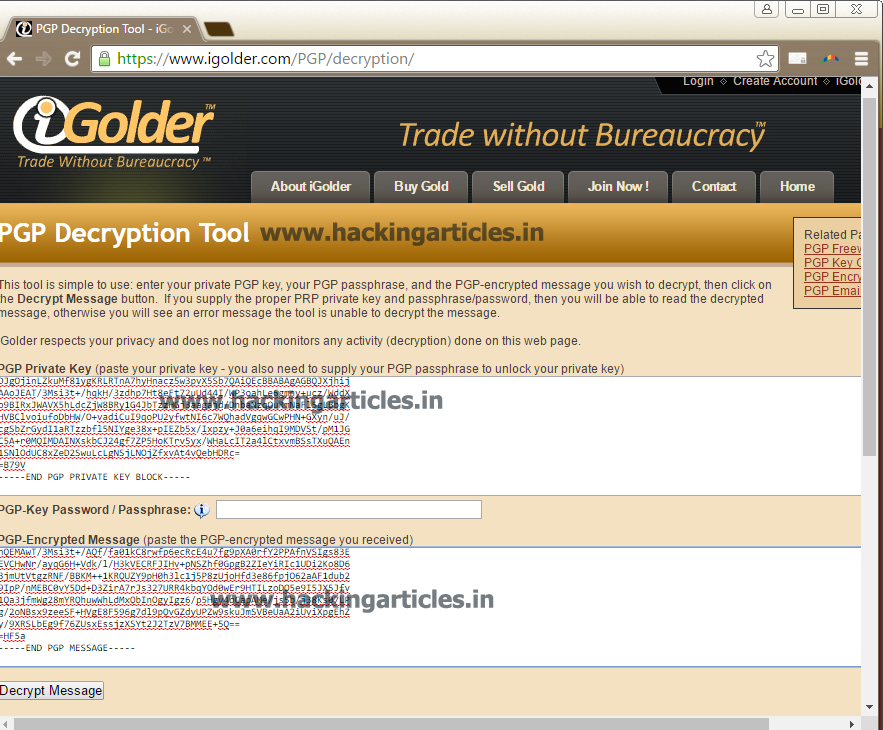
At last click on Decrypt message and your message will be decrypted.

Copyright @2024 Deepwatch. All Rights Reserved.